Cyber threats are evolving faster than traditional security measures can keep up. CTEM offers a proactive approach, shifting the focus from reactive defense to continuous risk assessment and mitigation. By identifying vulnerabilities before attackers exploit them, organizations can strengthen their security posture and stay ahead of evolving threats.
Cyber threats evolve faster than organizations can patch their systems. The traditional security approach—periodic vulnerability scans, annual penetration tests, and rigid compliance checklists—has proven inadequate against today’s sophisticated cyber adversaries.
Organizations have a diverse array of tools in place to monitor, manage, and defend a complex attack surface. In 2022, Gartner put out a reportOrganizations have long relied on reactive security measures, responding to breaches only after they occur. But in an era of advanced persistent threats and AI-driven attacks, waiting until an attack happens is no longer viable. CTEM shifts the focus from reactive defense to continuous, proactive risk assessment—identifying, prioritizing, and mitigating vulnerabilities before attackers exploit them.: “We used to try to prioritize what we would patch based on the criticality of the asset. The printer in my office might have a CVSS 10 on it, but it doesn’t matter if it catches on fire—it’s not going to affect the business like the point of sale might. But then, even in doing that, sometimes a low-value asset has all those elements that allow for a major jumping point to occur if it’s exposed.” Many cybersecurity professionals recognize that traditional security models struggle to keep pace with evolving threats. Properly implemented, CTEM offers a more dynamic approach, allowing organizations to assess their weaknesses from an attacker's perspective and address them proactively.CTEM is not just another security tool. In fact, Gartner stressed that it’s not really a tool at all—it’s a framework that ensures organizations stay ahead of threats. According to Gartner, which formally defined the concept, CTEM operates across five key stages:– Implementing security measures to address risks in real-time, ensuring the security posture remains strong amid evolving threats. This structured, iterative process ensures that security teams move beyond patch-and-pray tactics to a more informed, strategic approach.Many cybersecurity experts advocate for the widespread adoption of CTEM. Organizations need to move from periodic assessments to continuous security validation because attackers do not operate on a fixed schedule. Security teams must remain constantly vigilant. CTEM also addresses challenges posed by cloud migration and remote workforces. With identity-based attacks, supply chain vulnerabilities, and misconfigurations in SaaS applications increasing, organizations must go beyond traditional security controls. Companies operating in cloud environments often struggle with thousands of cloud instances and SaaS applications running at any given time. A single misconfiguration can expose critical data, and CTEM helps organizations catch these issues before they lead to security incidents.A Shift in Cybersecurity As cyber threats continue to outpace traditional security models, Continuous Threat Exposure Management is emerging as a game-changer. By offering a real-time, attacker-focused perspective on risk, CTEM enables organizations to close security gaps before they can be exploited. Cybersecurity today requires a dynamic approach to minimizing attack surfaces. CTEM represents an evolution in that respect, ensuring that organizations stay ahead of ever-changing threats and continuously enhance their security posture.Our community is about connecting people through open and thoughtful conversations. We want our readers to share their views and exchange ideas and facts in a safe space.Insults, profanity, incoherent, obscene or inflammatory language or threats of any kindContinuous attempts to re-post comments that have been previously moderated/rejectedAttempts or tactics that put the site security at riskProtect your community.
Cybersecurity CYBERSECURITY CONTINUOUS THREAT EXPOSURE MANAGEMENT PROACTIVE SECURITY ATTACKER-FOCUSED DEFENSE RISK MITIGATION
United States Latest News, United States Headlines
Similar News:You can also read news stories similar to this one that we have collected from other news sources.
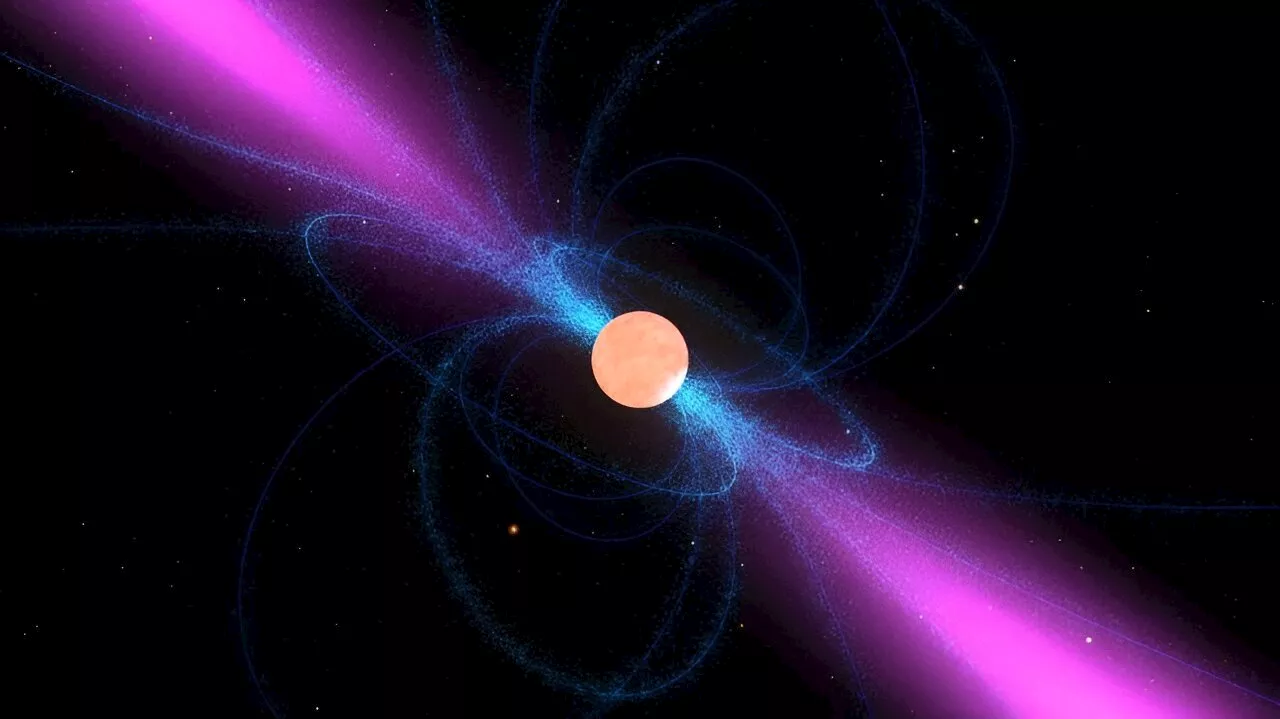 LIGO Fails to Find Continuous Gravitational Waves From PulsarsSpace and astronomy news
LIGO Fails to Find Continuous Gravitational Waves From PulsarsSpace and astronomy news
Read more »
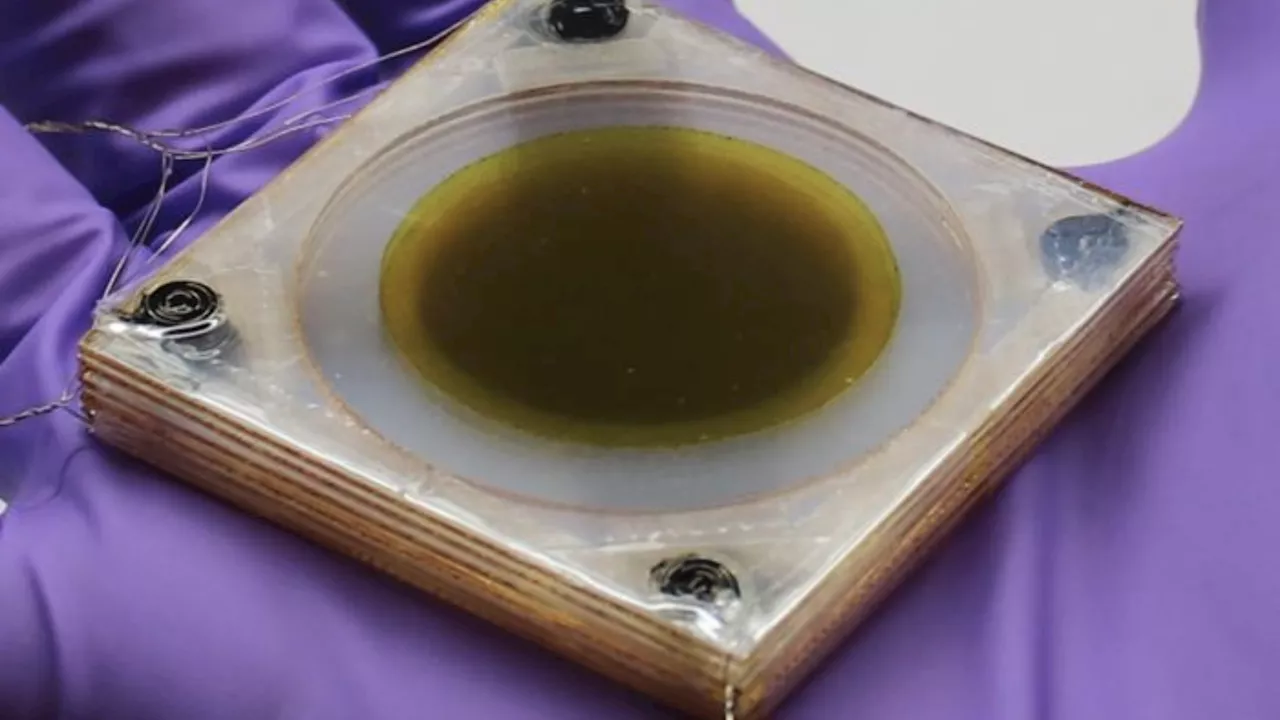 Scientists Develop Continuous Cooling Innovation Using Flexing Thin FilmsResearchers at UCLA have created a new cooling technology that utilizes the electrocaloric effect to continuously lower temperatures. The innovative design employs layers of flexing thin films that pump away heat when subjected to an electric field. In lab experiments, the prototype successfully reduced ambient temperatures by 16 degrees Fahrenheit continuously and up to 25 degrees at the heat source within 30 seconds.
Scientists Develop Continuous Cooling Innovation Using Flexing Thin FilmsResearchers at UCLA have created a new cooling technology that utilizes the electrocaloric effect to continuously lower temperatures. The innovative design employs layers of flexing thin films that pump away heat when subjected to an electric field. In lab experiments, the prototype successfully reduced ambient temperatures by 16 degrees Fahrenheit continuously and up to 25 degrees at the heat source within 30 seconds.
Read more »
 The Power of Continuous Advocacy: Building Careers and Driving ResultsThis article explores the essential role of managers as advocates for their employees, emphasizing the importance of continuous support and recognition. It highlights the pitfalls of a reactive approach to advocacy and underscores the benefits of prioritizing ongoing development and visibility for team members.
The Power of Continuous Advocacy: Building Careers and Driving ResultsThis article explores the essential role of managers as advocates for their employees, emphasizing the importance of continuous support and recognition. It highlights the pitfalls of a reactive approach to advocacy and underscores the benefits of prioritizing ongoing development and visibility for team members.
Read more »
 The Power of Continuous Employee AdvocacyThis article emphasizes the importance of managers advocating for their employees beyond just performance reviews and promotions. It argues for a proactive approach where managers continuously champion their team's growth by recognizing contributions, aligning efforts with organizational goals, and making their value visible to key stakeholders. The result is stronger engagement, higher performance, and a team ready to take on new challenges.
The Power of Continuous Employee AdvocacyThis article emphasizes the importance of managers advocating for their employees beyond just performance reviews and promotions. It argues for a proactive approach where managers continuously champion their team's growth by recognizing contributions, aligning efforts with organizational goals, and making their value visible to key stakeholders. The result is stronger engagement, higher performance, and a team ready to take on new challenges.
Read more »
 The Power of Continuous Advocacy: Building Careers and Driving ResultsThis article explores the importance of managers acting as advocates for their employees beyond performance reviews or promotions. It emphasizes the benefits of ongoing recognition, ensuring team efforts align with organizational goals, and making employee value visible to key stakeholders. The article highlights the positive ripple effects of such advocacy, including increased engagement, higher performance, and a team ready for new challenges.
The Power of Continuous Advocacy: Building Careers and Driving ResultsThis article explores the importance of managers acting as advocates for their employees beyond performance reviews or promotions. It emphasizes the benefits of ongoing recognition, ensuring team efforts align with organizational goals, and making employee value visible to key stakeholders. The article highlights the positive ripple effects of such advocacy, including increased engagement, higher performance, and a team ready for new challenges.
Read more »
 Beyond Promotion Cycles: The Power of Continuous Advocacy as a ManagerThis article emphasizes the importance of continuous employee advocacy by managers, going beyond reactive measures like promotion cycles. It highlights the benefits of recognizing contributions, aligning efforts with organizational goals, and making employee value visible to stakeholders. The author shares a real-life example of a manager who built a strong reputation as a 'Leader Maker' through consistent advocacy.
Beyond Promotion Cycles: The Power of Continuous Advocacy as a ManagerThis article emphasizes the importance of continuous employee advocacy by managers, going beyond reactive measures like promotion cycles. It highlights the benefits of recognizing contributions, aligning efforts with organizational goals, and making employee value visible to stakeholders. The author shares a real-life example of a manager who built a strong reputation as a 'Leader Maker' through consistent advocacy.
Read more »
