Hackers use malicious ads on streaming sites to spread malware, infecting nearly a million devices. Learn how they do it—and how to protect yourself.
This attack, originating from illegal streaming websites, highlights the increasing sophistication and reach of cyber threat s targeting consumers and businesses alike. The campaign, which was tracked as Storm-0408, used malicious advertisements embedded within movie frames to redirect users through multiple layers to malware hosted on GitHub and other platforms.
The attack appeared deceptively simple at first. Users seeking free access to movies on illegal streaming sites unwittingly initiated a complex chain of events. Rather than simple pop-up advertisements, the attackers embedded malicious code directly into the video streams themselves. This meant that as a user watched a film, hidden ads were silently working in the background, initiating a series of redirections. These redirections, sometimes four or five in number, were designed to obfuscate the attack's origin, making it incredibly difficult to trace. Users, unaware of the behind-the-scenes activity, were led through a digital maze, ultimately landing on sites that hosted malicious software. Notably, these malware-hosting sites included platforms like GitHub, which are typically considered trustworthy, allowing the attackers to exploit user confidence. Once the malware was downloaded, its primary objective was information theft. It began by gathering system information effectively taking a digital inventory of the compromised device. This was followed by the deployment of additional malware designed to steal sensitive data such as passwords, credit card details, documents, and browsing history.‘Severance’ Season 2, Episode 8 Recap And Review: I’m Not Sure How I Feel About This OneThis layered approach allowed the attackers to establish a persistent presence, maximizing their potential for data exfiltration. The impact was widespread, affecting not only individual consumers but also potentially compromising devices within business networks.The campaign's use of multiple redirections to reach the final malware payload highlights the sophistication of modern cyberattacks. These techniques are designed to evade detection and make it harder to trace the source of the attack.The ultimate goal of the campaign was to steal sensitive information from the compromised devices. This type of malware can have devastating consequences for individuals, leading to financial loss,Attackers are increasingly leveraging trusted platforms like GitHub, Dropbox, and Discord to host and distribute malware. By abusing these platforms' release infrastructures, they can deliver malicious payloads under the guise of legitimate software, making detection and prevention more challenging.," to carry out malicious activities. This approach allows them to blend in with normal system operations, reducing the likelihood of detection by security software.Many users turn to illegal streaming platforms for free content, but these sites are often riddled with malicious ads and scripts. Always use legitimate and trusted streaming services to minimize exposure to cyber threats. Consider using reputable ad blockers to reduce exposure to potentially malicious advertisements. While not foolproof, ad blockers can minimize the risk of encountering malvertising campaigns. Additionally, script blockers likeKeep an eye on your system's behavior. If you notice unusual slowdowns, excessive pop-ups, or unauthorized access attempts, it could be a sign of malware. Regularly check your task manager and review installed applications to spot and remove anything suspicious. Maintain regular backups of your critical data on external drives or secure cloud services. In the event of a malware infection, having backups ensures you can restore your information without paying ransom or losing valuable data.Avoid clicking on links or ads from unknown sources. Make sure to use a reputable antivirus program to protect your system. A good antivirus can detect and remove malware before it causes damage.
Streaming Malware Cyber Threat Malicious Ads Malware Campaign Data Theft Online Security Github Malware Security Threats Cybersecurity Tips
United States Latest News, United States Headlines
Similar News:You can also read news stories similar to this one that we have collected from other news sources.
 JWST Uncovers Hidden Asteroid Population, Giving Scientists New Tools to Protect EarthThe James Webb Space Telescope (JWST), originally designed to study the cosmos, is revealing crucial information about a population of small main-belt asteroids. This discovery provides valuable insights for planetary defense efforts, as these smaller asteroids can pose a significant threat to Earth.
JWST Uncovers Hidden Asteroid Population, Giving Scientists New Tools to Protect EarthThe James Webb Space Telescope (JWST), originally designed to study the cosmos, is revealing crucial information about a population of small main-belt asteroids. This discovery provides valuable insights for planetary defense efforts, as these smaller asteroids can pose a significant threat to Earth.
Read more »
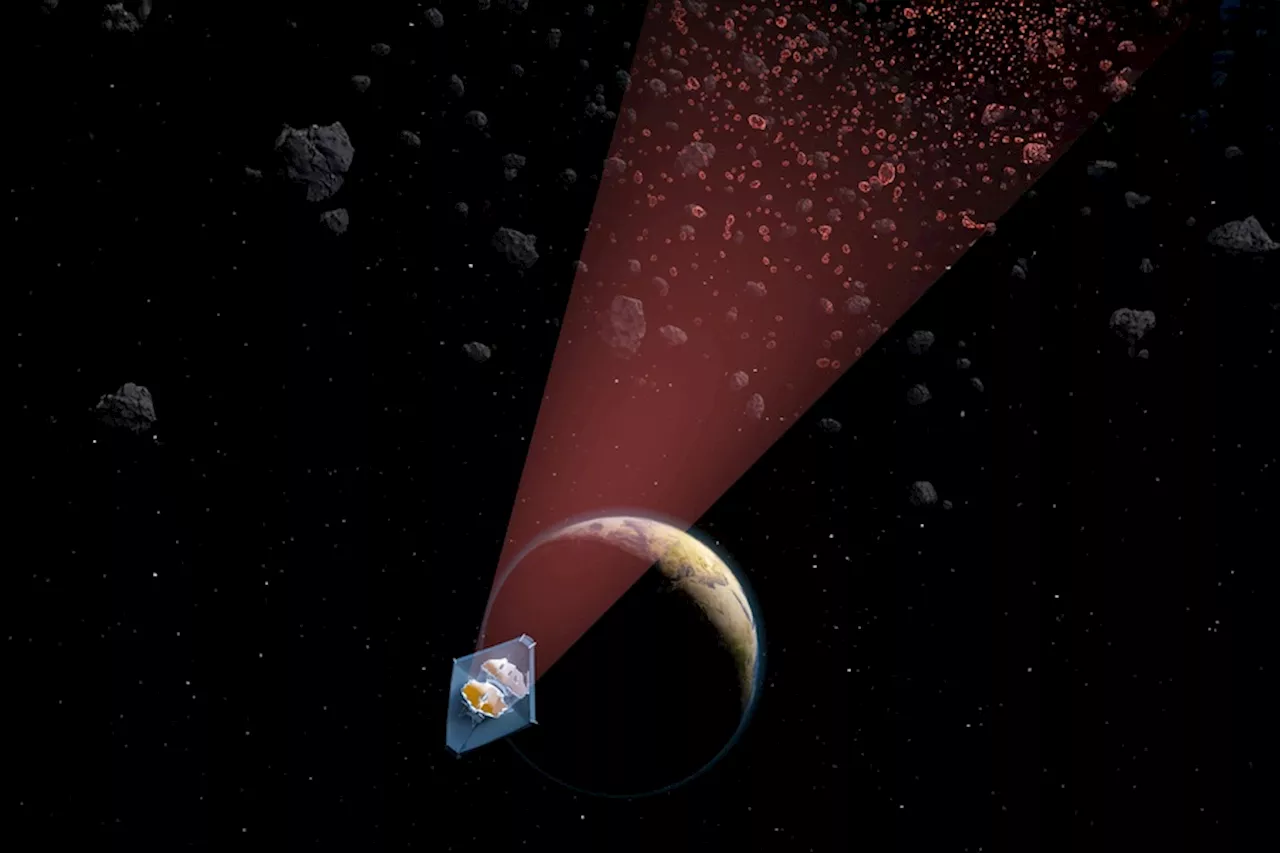 JWST Uncovers New Population of Small Asteroids, Boosting Planetary DefenseNASA's James Webb Space Telescope, initially designed to study the cosmos, is proving instrumental in identifying small asteroids that could pose a threat to Earth. The telescope's powerful infrared capabilities allow it to detect these smaller objects, which are more difficult to spot with traditional methods.
JWST Uncovers New Population of Small Asteroids, Boosting Planetary DefenseNASA's James Webb Space Telescope, initially designed to study the cosmos, is proving instrumental in identifying small asteroids that could pose a threat to Earth. The telescope's powerful infrared capabilities allow it to detect these smaller objects, which are more difficult to spot with traditional methods.
Read more »
 FBI Uncovers Unseen JFK Assassination Files, Fueling New SpeculationThe FBI has unearthed a cache of previously unknown files related to the assassination of President John F. Kennedy, rekindling interest in the enduring mystery. The agency is transferring the documents to the National Archives for declassification, sparking speculation about their potential contents.
FBI Uncovers Unseen JFK Assassination Files, Fueling New SpeculationThe FBI has unearthed a cache of previously unknown files related to the assassination of President John F. Kennedy, rekindling interest in the enduring mystery. The agency is transferring the documents to the National Archives for declassification, sparking speculation about their potential contents.
Read more »
 Vitalik Buterin Shares Reasons to Adopt Higher L1 Gas LimitEthereum's Vitalik Buterin uncovers why scaling layer-1 protocols is crucial
Vitalik Buterin Shares Reasons to Adopt Higher L1 Gas LimitEthereum's Vitalik Buterin uncovers why scaling layer-1 protocols is crucial
Read more »
 Microsoft to Shut Down Skype, Replace it with Free Microsoft TeamsMicrosoft is discontinuing Skype in favor of its free communication and collaboration platform, Microsoft Teams.
Microsoft to Shut Down Skype, Replace it with Free Microsoft TeamsMicrosoft is discontinuing Skype in favor of its free communication and collaboration platform, Microsoft Teams.
Read more »
 Microsoft suggests four fixes for ancient Microsoft Store bugMicrosoft finally releases four solutions to the old 0x80131500 error that has been around since 2019. What are those official solutions?
Microsoft suggests four fixes for ancient Microsoft Store bugMicrosoft finally releases four solutions to the old 0x80131500 error that has been around since 2019. What are those official solutions?
Read more »
