I am Editor-in-Chief of TechSpective. I have a passion for technology and gadgets and a desire to help others understand how technology can affect or improve their lives.
Cloud security remains a paramount concern for enterprises. Traditional security practices, which primarily focus on visibility and detection, are no longer sufficient to combat the sophisticated threats targeting cloud environments.
The complexity and variability inherent in cloud infrastructures demand a comprehensive security strategy that transcends simple remediation., CEO and co-founder of ZEST Security about how enterprises can adopt effective risk mitigation and resolution strategies to enhance their security posture and the vision for ZEST moving forward.Historically, cloud security efforts have been centered around gaining visibility into potential threats and vulnerabilities. Tools were developed to identify issues such as misconfigurations and vulnerabilities, providing security teams with a detailed view of their security landscape. However, this approach has significant limitations. Shimol explained, “Visibility is just the first step. Knowing about your problems without having an efficient way to resolve them leaves organizations vulnerable and frustrated.” According to Shimol, the shift towards resolution-focused solutions is pivotal for effective cloud security. Rather than merely identifying risks, he emphasizes resolving these issues promptly and effectively. This shift is crucial in reducing the attack surface and preventing known vulnerabilities from being exploited repeatedly.Trump Vs. Harris 2024 Polls: Latest Surveys Show A Virtual Tie After Biden Drops Out We also talked about the integration and collaboration between security and DevOps teams. Traditional silos between these teams often lead to inefficiencies and delays in addressing security issues. “Security cannot change anything in the cloud without the involvement of DevOps,” noted Shimol. “This collaboration is essential to ensure that security measures are implemented effectively.” By fostering a collaborative environment, organizations can streamline the process of identifying and resolving vulnerabilities. He believes this approach not only enhances security but also ensures that DevOps practices are aligned with overarching security goals.Artificial Intelligence and automation are inextricably woven throughout cybersecurity, and cloud security is no exception. These technologies enable organizations to scale their security efforts and respond to threats more rapidly. The ZEST Security platform uses Generative AI to craft automated resolution paths and reduce the time and effort required for manual remediation. By automating the identification and resolution of vulnerabilities, AI enhances the effectiveness and efficiency of security operations. “AI allows us to run infinite options and provide the best resolution paths,” explains Shimol. “This capability is transforming how organizations approach cloud security, making it possible to address issues at scale and with greater precision.”The financial implications of cloud security strategies are a major consideration for enterprises. Traditional methods of manual remediation are not only time-consuming but also costly. On average, it takes 30-60 days to remediate a single cloud security risk, with 80% of resolved risks resurfacing shortly after remediation. Implementing automated resolution and mitigation strategies can lead to significant cost savings. By reducing the operational burden on security and DevOps teams, organizations can allocate resources more efficiently and improve their overall security posture.A comprehensive security strategy must go beyond simple remediation to include proactive risk mitigation. This involves leveraging existing tools and infrastructure to reduce the exploitability of vulnerabilities, even when they cannot be immediately fixed. ZEST Security’s platform exemplifies this approach by providing both remediation and mitigation options. “Mitigation is about making it harder for threat actors to exploit vulnerabilities,” says Shimol. “By using the cloud’s native security controls and our automated resolution paths, we can reduce risks from critical to medium or low, ensuring that our clients are better protected.” Shimol described how this comprehensive approach addresses the inherent complexity of cloud environments, offering a more robust defense against emerging threats.The landscape of cloud security is continually evolving, and enterprises must adapt by adopting comprehensive strategies that go beyond mere remediation. For CISOs and security professionals, embracing these innovative approaches is crucial to staying ahead of the curve and ensuring the resilience of their cloud environments. By moving beyond traditional practices and leveraging advanced technologies, enterprises can build a more secure and efficient future.Our community is about connecting people through open and thoughtful conversations. We want our readers to share their views and exchange ideas and facts in a safe space.Insults, profanity, incoherent, obscene or inflammatory language or threats of any kindContinuous attempts to re-post comments that have been previously moderated/rejectedAttempts or tactics that put the site security at riskProtect your community.
Mitigation Remediation Detection Resolution AI Automation Snir Ben Shimol Cybersecurity ZEST Security
United States Latest News, United States Headlines
Similar News:You can also read news stories similar to this one that we have collected from other news sources.
 Teck, Taku River Tlingit First Nation, BC partner on Tulsequah Chief mine remediationNo 1 source of global mining news and opinion
Teck, Taku River Tlingit First Nation, BC partner on Tulsequah Chief mine remediationNo 1 source of global mining news and opinion
Read more »
 Career Risk Traps Advisors Into Taking on Excess Risk With Your MoneyStocks Analysis by Lance Roberts covering: S&P 500. Read Lance Roberts's latest article on Investing.com
Career Risk Traps Advisors Into Taking on Excess Risk With Your MoneyStocks Analysis by Lance Roberts covering: S&P 500. Read Lance Roberts's latest article on Investing.com
Read more »
 36-Hour Window Safe for Globe Injury Repair, Risk Grows AfterDelaying the repair of open globe injuries beyond 36 hours increases the risk for endophthalmitis.
36-Hour Window Safe for Globe Injury Repair, Risk Grows AfterDelaying the repair of open globe injuries beyond 36 hours increases the risk for endophthalmitis.
Read more »
 Enhancing Risk Mitigation And IT SecurityI am Editor-in-Chief of TechSpective. I have a passion for technology and gadgets and a desire to help others understand how technology can affect or improve their lives.
Enhancing Risk Mitigation And IT SecurityI am Editor-in-Chief of TechSpective. I have a passion for technology and gadgets and a desire to help others understand how technology can affect or improve their lives.
Read more »
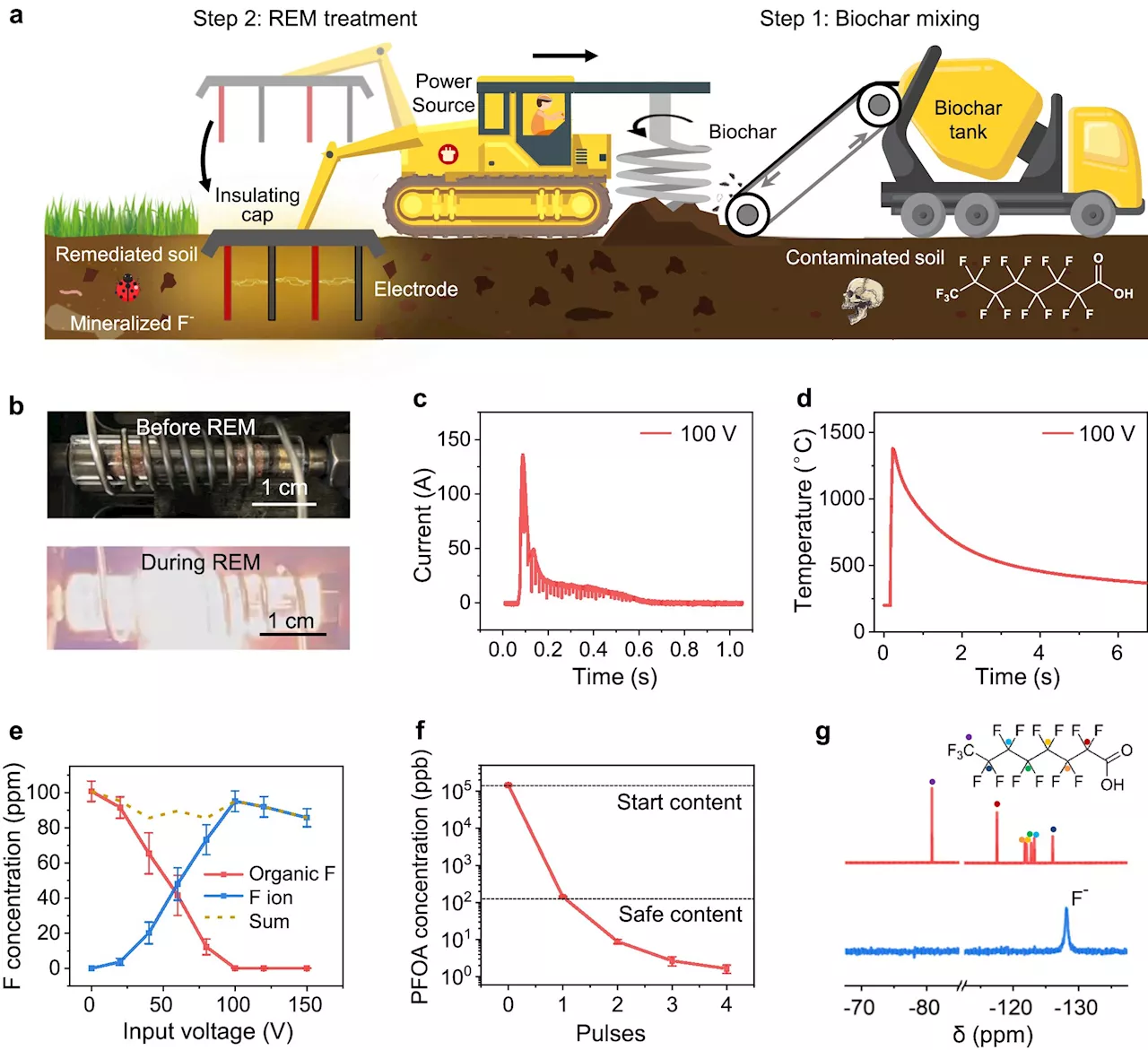 Electrothermal mineralization process offers more environmentally friendly, cost-effective method for soil remediationRice University chemist James Tour has led a research team to develop a rapid electrothermal mineralization (REM) process, which in seconds can remediate the accumulation of synthetic chemicals that can contaminate soil and the environment. The study was published in Nature Communications on July 20.
Electrothermal mineralization process offers more environmentally friendly, cost-effective method for soil remediationRice University chemist James Tour has led a research team to develop a rapid electrothermal mineralization (REM) process, which in seconds can remediate the accumulation of synthetic chemicals that can contaminate soil and the environment. The study was published in Nature Communications on July 20.
Read more »
 Researchers develop more environmentally friendly and cost-effective method for soil remediationChemists have developed a rapid electrothermal mineralization (REM) process, which in seconds can remediate the accumulation of synthetic chemicals that can contaminate soil and the environment.
Researchers develop more environmentally friendly and cost-effective method for soil remediationChemists have developed a rapid electrothermal mineralization (REM) process, which in seconds can remediate the accumulation of synthetic chemicals that can contaminate soil and the environment.
Read more »
